HIPAA Security Checklist: A Complete Compliance Guide for Healthcare
The blog offers a HIPAA security checklist for healthcare organizations, entities it covers, and PHI, to achieve full HIPAA compliance. It covers the key safeguards, like technical and administrative, a step-by-step compliance process, and best practices to boost data security.
.png?width=670&height=445&name=AI%20Cybersecurity%20Threats%20(6).png)
Though the integration of AI in healthcare solutions and other advanced technologies has streamlined the processes around healthcare, what about the data security concerns?
Are you aware that in 2025 alone, there were around 60 data breaches every month in the healthcare sector? It exposed the most critical patient-sensitive information and their records.
These numbers clearly state that healthcare data is vulnerable. Moreover, with the integration of EHRs, cloud platforms, AI, and more, the risk of exposing protected health information increases.
For healthcare organizations and businesses, it is no longer simply about meeting the regulatory requirements under HIPAA, but is also about safeguarding patient trust while navigating the complex compliance landscape.
And that is where the need for a well-defined and actionable HIPAA security checklist becomes vital. It allows organizations to implement the right kind of physical and technical safeguards, conduct risk assessment, and ultimately build a strong HIPAA IT compliance program.
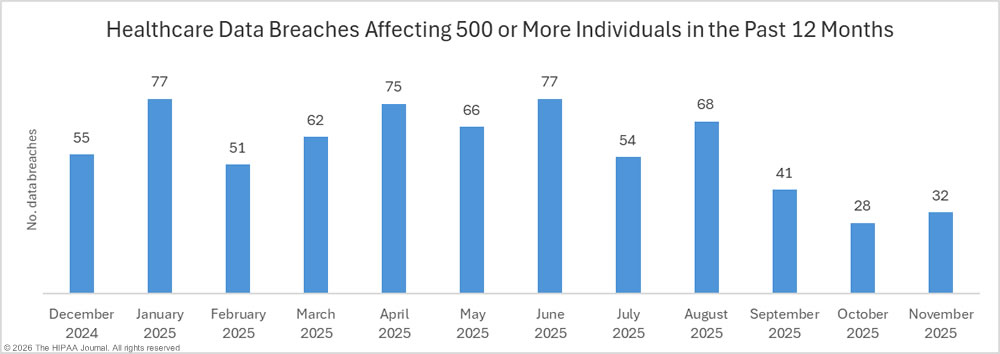
Source: Hipaajournal
 Generate
Key Takeaways
Generating...
Generate
Key Takeaways
Generating...

- A structured HIPAA compliance checklist is vital to implement physical, technical, and other safeguards.
- Regular risk assessments and audits help maintain a strong compliance posture.
- Secure software development and HIPAA compliance help protect ePHI.
- Aligning AI healthcare solutions with compliance helps with innovation without compromising data security.
What is HIPAA?
Health Insurance Portability and Accountability Act (HIPAA) is a U.S. federal law enacted in 1996 that protects the privacy and security of patients’ medical information and regulates how healthcare organizations collect, store, and share protected health data.
It establishes standards for safeguarding Protected Health Information (PHI) and ensures that healthcare providers, insurers, and related organizations handle patient data securely and confidentially.
Understanding HIPAA’s Key Rules
Understanding the vital rules and regulations in HIPAA helps build a strong HIPAA compliance program and also ensures that sensitive information is protected.
1. HIPAA Privacy Rule: This privacy rule helps set the national standards and protects PHI to ensure patient privacy. The HIPAA-compliant officer oversees compliance with these standards.
2. HIPAA Security Rule: It focuses on protecting the health information via physical, technical, and administrative measures. The administrative measures train the employees and hire security officers. The physical safeguards the facilities and devices, and the technical safeguards the access control measures via encryption.
3. HIPAA Breach Notification Rule: It requires covered entities to report the security incidents and breaches that affect PHI. This ensures more transparency and accountability.
The Ultimate HIPAA IT Security Checklist
To achieve complete HIPAA compliance, businesses need a comprehensive approach that covers the administrative, physical, and technical safeguards. Here is a checklist that offers complete insights and allows healthcare providers to shield their protected healthcare information and maintain compliance.
Administrative Safeguards
Administrative safeguards rely on policies and procedures that ensure ongoing compliance and data protection across the healthcare sector.
Appoint a HIPAA Security Officer: The key role of the HIPAA security officer is to manage the efforts of compliance, maintain the program, and ensure the security measures are imposed properly.
Establish Policies and Procedures: Establishing and documenting the policies in the right way is vital to managing the security incidents, having access controls, and defining the responsibilities for covered entities.
Conduct HIPAA Training & Awareness Programs: With regular HIPAA training, businesses ensure that staff can understand the obligations regarding confidentiality, integrity, and PHI availability. This helps prevent HIPAA violations efficiently.
Perform Regular Risk Assessment: Check if there are any potential vulnerabilities in the electronic information system, assess the threats that are anticipated, and take necessary measures to ensure compliance.
Define Security Incident Reporting Processes: With accurate procedures for security incident reporting, businesses can ensure they are able to quickly respond to breaches. This also allows them to stop unauthorized access and align with the HIPAA breach notification rule.
Maintain HIPAA Compliance Program: Continuous monitoring, internal audits, and compliance efforts ensure the organization adapts to evolving HIPAA requirements and sustains long-term HIPAA compliance.
Physical Safeguards
Physical safeguards protect the infrastructure that has the entire process:
Limit Physical access to systems: It controls entry to servers, workstations, and offers storage facilities. It prevents unauthorized access to individually identifiable health information.
Secure Electronic Information System: It helps ensure that all electronic information systems remain physically protected and can be maintained to prevent data loss.
Monitor Physical Access Control: Access control can be managed with logs and access management tools that help track who actually has access to sensitive domains. It is vital to support the accountability act requirements.
Implement Plan for Disaster Recovery: Recovery plans and establishing the right procedures can help maintain the availability and confidentiality of PHI. It is vital in case of emergencies or system failures.
Technical Safeguards
Technical safeguards help protect data within the electronic systems and software applications:
Robust Access Control: Implementing role-based access control, multifactor authentication, and restricted permissions based on user roles helps restrict any unauthorized access to ePHI.
Encrypted Electronic Protected Health Information: This helps encrypt ePHI in both transit and at rest. It prevents any unauthorized disclosure in case of breach.
Implement Strict Security Control: Ensure safe and secure data handling. Audit trails and logging of access to sensitive information, supporting HIPAA audit needs.
Ensure Software Security Capability: Relying on HIPAA-compliant software that has all the security features, secure APIs, and vulnerability management helps protect the electronic information system.
Protection against Threats: Ensure to continue monitoring and mitigating the hacking risks, malware, insider threats, and more. This helps ensure alignment with security rule requirements.
Related Read : Your Complete Guide to Healthcare Software Development Success in 2026
HIPAA Compliance Checklist for Software Development
For organizations handling sensitive health information, it is important to align the software practices with compliance, and here is the complete checklist to follow.
Secure SDLC for HIPAA-Compliant Applications
A secure SDLC is vital and is the foundation of HIPAA compliance needs. This means the entire cycle needs to be taken care of, from design to implementation and maintenance as well. Teams must clearly define the policies and procedures, conduct assessments, and implement these safeguards at every stage of the cycle. Also, conduct regular audits and testing to identify if there are any vulnerabilities and allow for easy handling.
Data Encryption & API Security
The healthcare information must be protected with strong encryption. It should be taken care of at rest and in transit. Also, secure APIs are vital, especially when the systems interact with third-party platforms. Ensure the implementation of authentication protocols and a secure data exchange. This ensures that sensitive data and information are protected across the electronic information system.
Role-Based Access Controls
To limit the exposure of data, ensure a strong role-based access control for the users. This implementation ensures that only authorized users are allowed to access the reports and sensitive information, while restricting access to unauthorized users. This aligns with the HIPAA security checklist and helps ensure that the information remains confidential. With multifactor authentication and management of data, the access restrictions are further improved.
Logging & Security Incident Reporting
With a strong mechanism for logging, information tracking across all system activities involving PHI is easy. Detailed audit logs help support HIPAA audit readiness and allow for quick detection of abnormalities. Healthcare organizations should be clearly able to define security incident reporting and breach notifications for effective reporting of threats.
Aligning AI Healthcare Solutions with Compliance
Building AI for healthcare is continuously rising, and therefore, it becomes vital to ensure it remains compliant with HIPAA. Train AI models as per the compliance requirements and deploy them with strict data governance policies. This ensures there is no unauthorized access and the data remains secure. Smart validation and transparency in AI decision-making ensure trust and alignment with HIPAA regulations.
Unlock the Future of Compliant Healthcare AI
Discover how to build secure, scalable, and compliant systems with AI.
Handling Business Associates
Third-party vendors that handle PHI qualify as a business associate of HIPAA. It is vital for healthcare organizations to establish business associate agreements that clearly define the responsibilities for security, compliance efforts, and the handling of data breaches. Ensuring that all the business associates follow the same compliance checklist is vital to maintain the end-to-end compliance ultimately.
Who Needs to Follow This Checklist?
The security checklist applies to businesses that handle and process critical healthcare information. There are different stakeholders who must follow this checklist and ensure HIPAA compliance is met.
Healthcare Providers: Hospitals or clinics that manage the healthcare information, test reports, and sensitive patient data must implement stringent rules for security. They must also ensure robust privacy measures to stay compliant with HIPAA.
Healthcare Organizations: This covers the insurance agents, healthcare systems, and businesses that handle electronic healthcare information. It is important for them to maintain a strong HIPAA compliance program and overall compliance posture.
SaaS & Software Development Companies: The companies building and managing healthcare applications must ensure to follow HIPAA compliance standards and implement technical safeguards to stay compliant. This helps ensure that the platforms remain protected with the sensitive information via software security capabilities.
Business associates & HIPAA business associate agreements: Third-party vendors and service partners that access PHI should comply with HIPAA regulations and sign the business associate agreement. This ensures more accountability and data security that aligns with the compliance expectations.
If you are one who falls into the category, ensure to follow a structured HIPAA compliance checklist and avoid any costly violations.
Related Read: The Future of Business Intelligence in Healthcare
Step-by-Step HIPAA Compliance Process
Maintaining HIPAA compliance is a process that needs a structured execution and improvement. Here is an approach that helps you guide through your journey.
Initial Risk Assessment
Identify the vulnerabilities first with a comprehensive risk assessment process. Identifying the issues in the system that handles protected health information and electronic health information is equally important. The step helps uncover all the potential threats and is the foundation of the HIPAA compliance program.
Gap Analysis
The next step is evaluating and identifying the gaps between your current compliance and the actual HIPAA requirements. Identify gaps in technical, administrative, and physical safeguards, and also the missing policies and procedures. This helps with a better understanding of what needs to be addressed and helps you achieve HIPAA in an effective way.
Get Your HIPAA Compliance Gap Assessed
Not sure where you stand? Identify risks, gaps, and quick wins in minutes.
Implement Security and Privacy Measures
Implement strong security controls and measures, such as access control, encryption, and security controls, along with a clean security incident reporting process. Also, ensure it aligns with HIPAA security rules and privacy rules.
Conduct Internal Audits
Regularly conducting audits is essential to ensure HIPAA compliance is met. HIPAA needs internal audits to validate compliance. These audits can seamlessly monitor the compliance efforts and detect weaknesses. This ensures adherence to established processes and procedures.
Continuous Monitoring & Improvement
HIPAA compliance maintenance needs ongoing efforts like real-time monitoring, regular updates to security measures, and HIPAA training on a continuous basis. This ensures a long-term protection and compliance posture in the evolving threat landscape.
|
Challenge |
Description |
Impact on HIPAA Compliance |
|
Managing Compliance Processes |
Organizations have issues with compliance processes across different safeguards. |
May lead to gaps in HIPAA compliance needs and a weak posture |
|
Lack of Security Awareness & Training |
Poor HIPAA training and low security awareness |
Increased risk of violations and mishandling of protected health information (PHI) |
|
Incomplete Risk Assessment |
Inability to conduct regular security risk assessments |
Makes the system vulnerable to anticipated threats |
|
Weak Access Controls |
Poor access control implementation and user permissions |
Unauthorized access to ePHI |
|
Wrong Security Incident Reporting |
Lack of structured security incident reporting |
Slows down the process of addressing breaches |
|
Third-Party Compliance Risks |
The business associate becomes mismanaged and misses the agreement |
Rises exposure to compliance risks across entities and business associates |
|
Outdated Policies and Procedures |
Failure to update the policies with evolving regulations |
Weakens the overall HIPAA compliance program |
|
Poor Data Security Measures |
Poor data security and a lack of encryption |
Rises risk of breaches that involve individually identifiable health information |
Best Practices to Maintain HIPAA Compliance
Healthcare businesses must put continuous efforts and ensure strong monitoring to maintain HIPAA compliance. Here are the best practices that help sustain a smart compliance program:
Regular HIPAA Audit
Conduct regular HIPAA audit processes that can evaluate the compliance posture and identify gaps in the effectiveness of HIPAA. With regular audits, healthcare organizations can detect vulnerabilities much earlier. It also helps support the ongoing compliance efforts.
Update Policies and Procedures
Review and update policies regularly to ensure staying competitive in the technological landscape. Also, keep the documentation current and up-to-date to maintain HIPAA compliance and ensure the security measures are actually effective.
Continuous HIPAA Compliance Efforts
Treat compliance as an ongoing process rather than a one-time activity. Regular risk assessments and process improvements are necessary to adapt to new threats and meet evolving HIPAA requirements.
Strengthen Data Security Measures
Implement strong practices for data security like encryption, backups, and monitoring in real-time to protect the sensitive health information and electronic health information. Use strong safeguards to defend against anticipated threats and reduce the risk of breaches.
Train Employees Consistently
Employees must possess the knowledge and awareness of HIPAA compliance and the related program. They must be trained regularly so that they understand how to actually handle the sensitive information securely. Training staff is critical to prevent security incidents and support the overall compliance efforts.
Conclusion
The healthcare sector is ever-evolving with improved digital transformation, and therefore, it becomes vital to maintain strict HIPAA compliance. It has become the foundation to ensure a long-term trust from patients and other stakeholders. From implementing all the safeguards to conducting regular audits and monitoring, a structured approach helps organizations stay compliant.
For businesses leveraging AI healthcare solutions, the stake is even higher. Integrating AI in healthcare offers a better commitment to security, regular alignment, and a resilient compliance program. If you are looking forward to building a future-ready healthcare system, you can reach out to us.


Frequently Asked Questions
Have a question in mind? We are here to answer. If you don’t see your question here, drop us a line at our contact page.
What is Included in a HIPAA IT security checklist?
![]()
It basically covers all the technical, administrative, and physical safeguards like access control, encryption, and secure electronic information systems. It also helps ensure that healthcare organizations remain protected from anticipated threats and supports the confidentiality of sensitive healthcare data.
How is a HIPAA compliance checklist for software development different from general compliance?
![]()
It focuses on building a HIPAA-compliant application and includes SDLC practices, software security capabilities, incident reporting, and more. It ensures all the systems can handle protected health information and meet HIPAA IT compliance standards.
Who is responsible for ensuring HIPAA compliance within an organization?
![]()
The HIPAA compliance officer is responsible for ensuring compliance within the organization. These roles and responsibilities ensure that proper procedures are followed, manage compliance efforts, and lead initiatives effortlessly.
Is there a free HIPAA compliance checklist available for organizations?
![]()
Yes, many organizations offer a free HIPAA compliance checklist to help businesses assess their current compliance posture. These checklists usually cover administrative, physical, and technical safeguards, risk assessment, and breach notification procedures.


%201-1.webp?width=148&height=74&name=our%20work%20(2)%201-1.webp)